Usage Examples
mhost has many commands, each with a short alias: lookup (l), domain-lookup (domain), discover (d), check (c), trace (t), propagation (prop), verify (v), diff, and info.
Simple Lookup
mhost l github.com
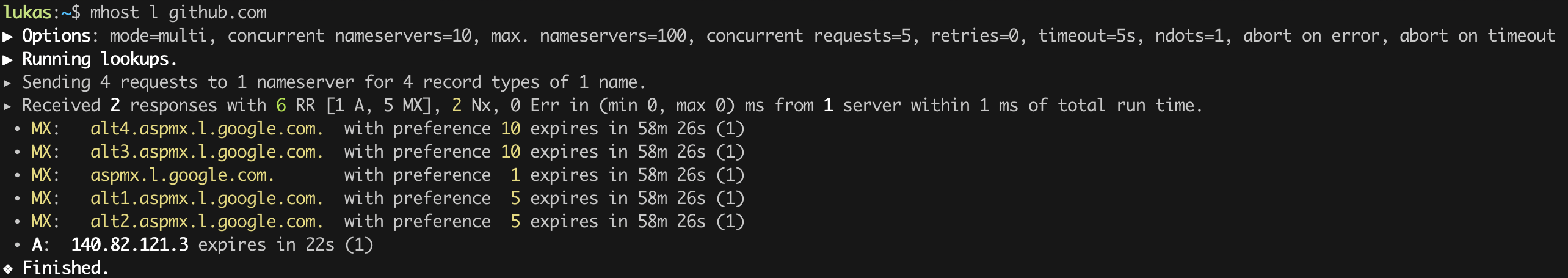
Uses your system nameservers and queries the default record types (A, AAAA, CNAME, MX).
More nameservers, more answers
mhost -p l github.com
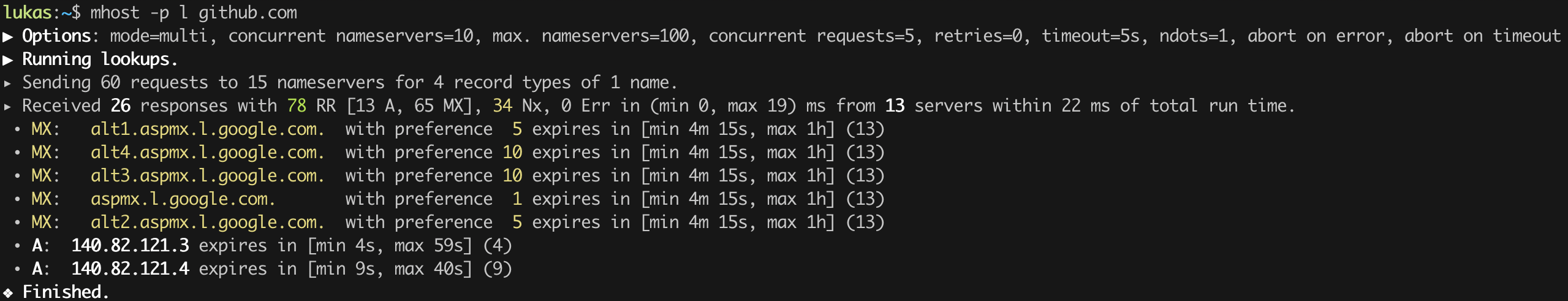
-p adds 84 predefined public nameservers from Cloudflare, Google, Quad9, Mullvad, Wikimedia, and DNS4EU. More servers means more confidence that you're seeing the full picture.
Thousands of nameservers
mhost server-lists public-dns -o servers.txt
mhost --limit 6000 --max-concurrent-servers 1000 --timeout 1 -f servers.txt l www.github.com
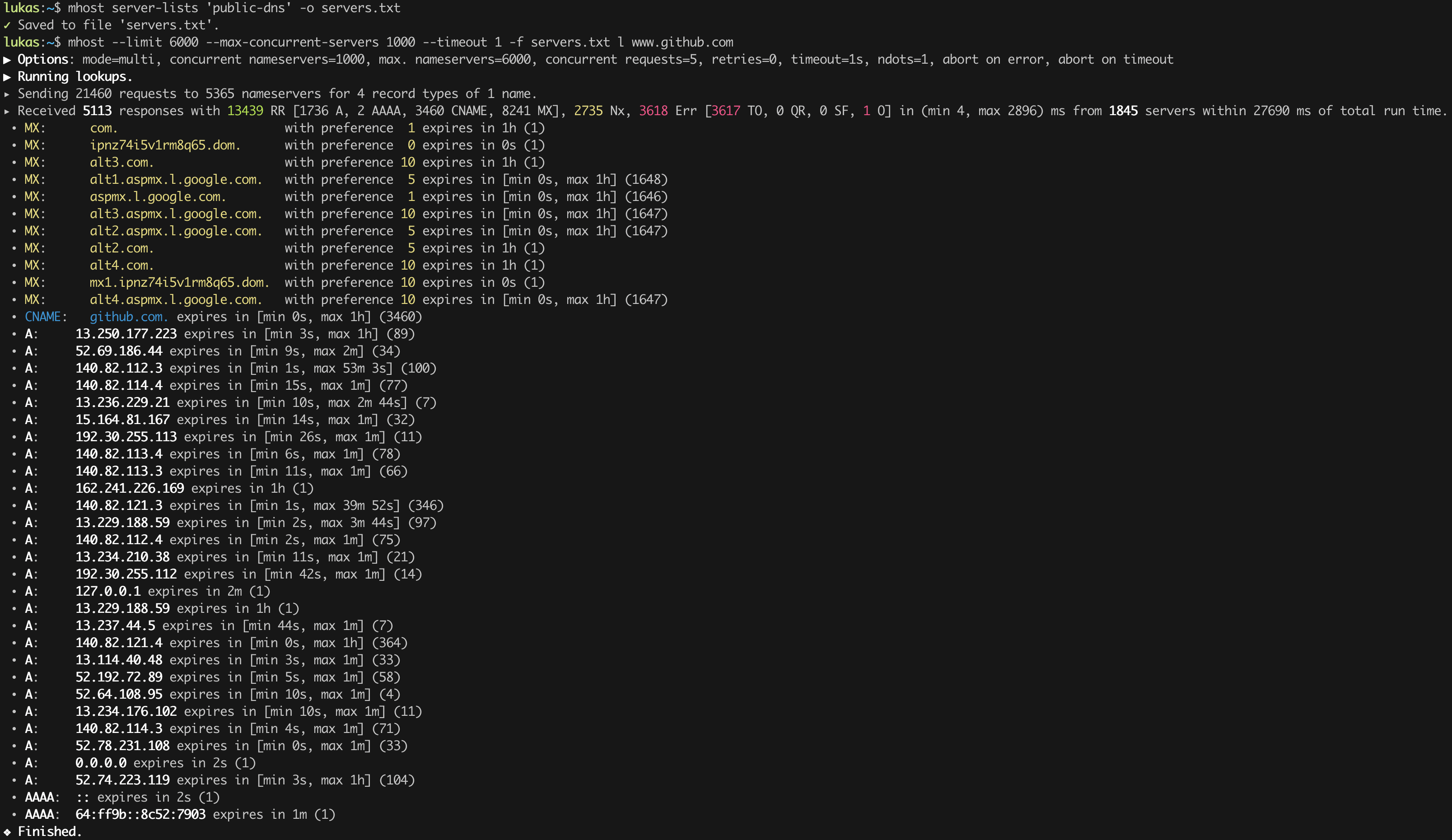
Download a community-maintained list of public resolvers, then fire queries at all of them. These settings are intentionally aggressive -- mhost defaults are much more cautious.
All four protocols at once
mhost \
-s 1.1.1.1 \
-s tcp:1.1.1.1 \
-s tls:1.1.1.1:853,tls_auth_name=cloudflare-dns.com \
-s https:1.1.1.1:443,tls_auth_name=cloudflare-dns.com,name=Cloudflare \
l github.com
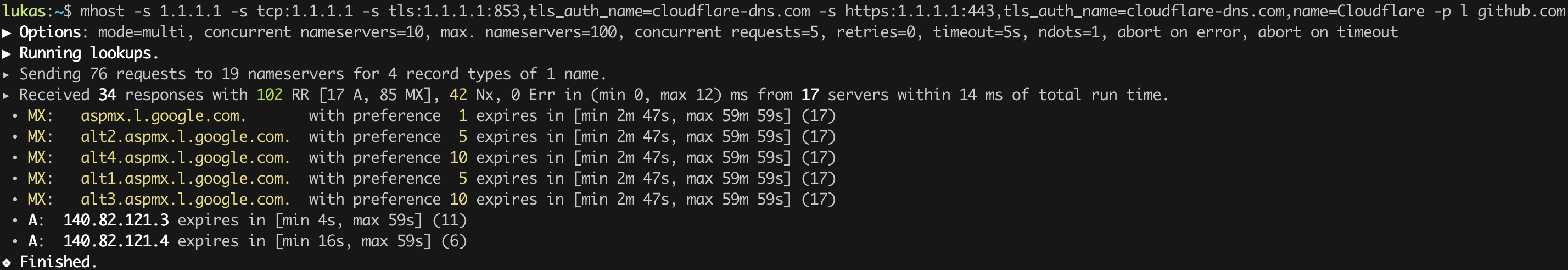
Nameserver spec format: protocol:host:port,tls_auth_name=hostname,name=label
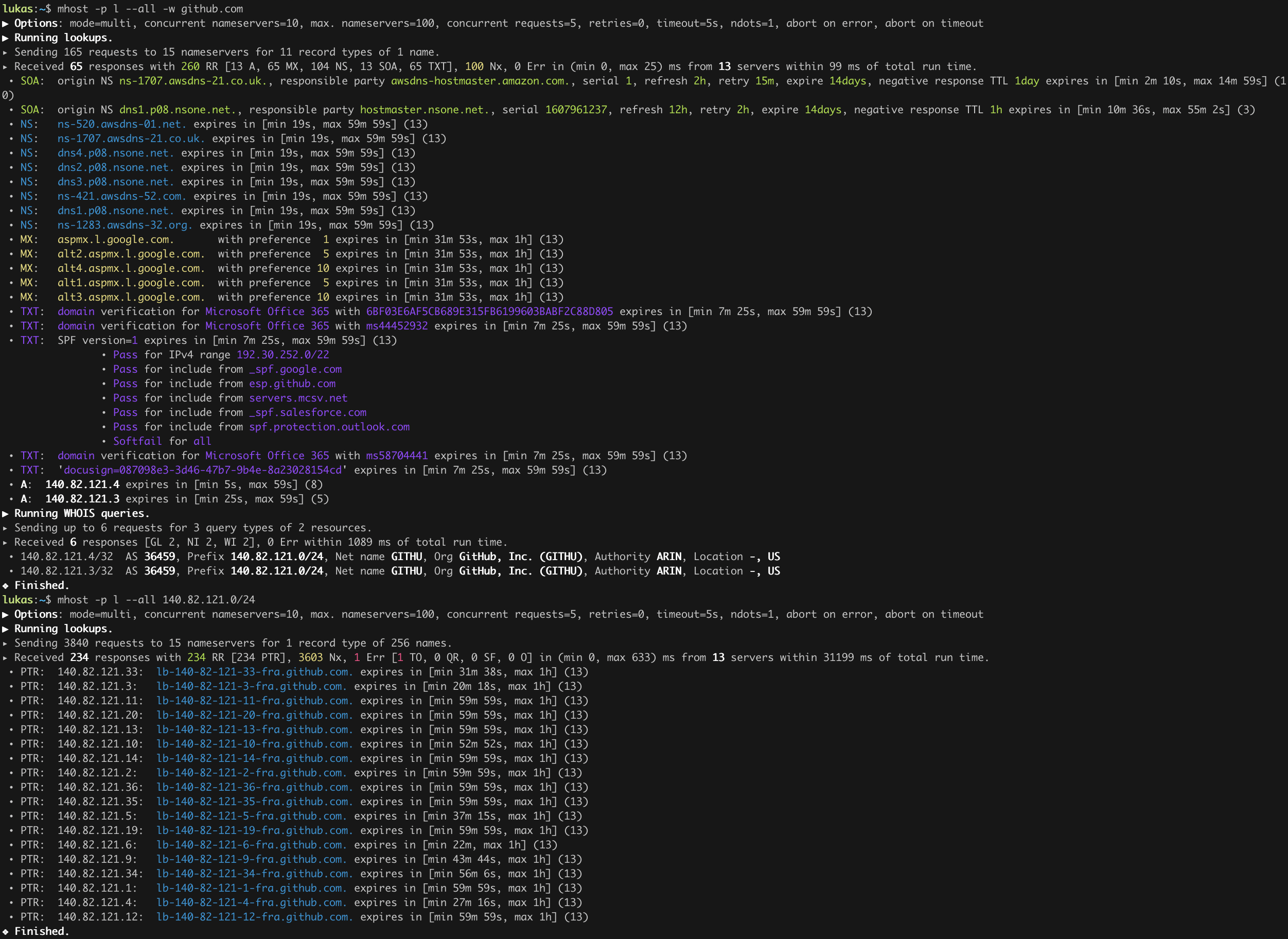
All record types + WHOIS
mhost -p l --all -w github.com
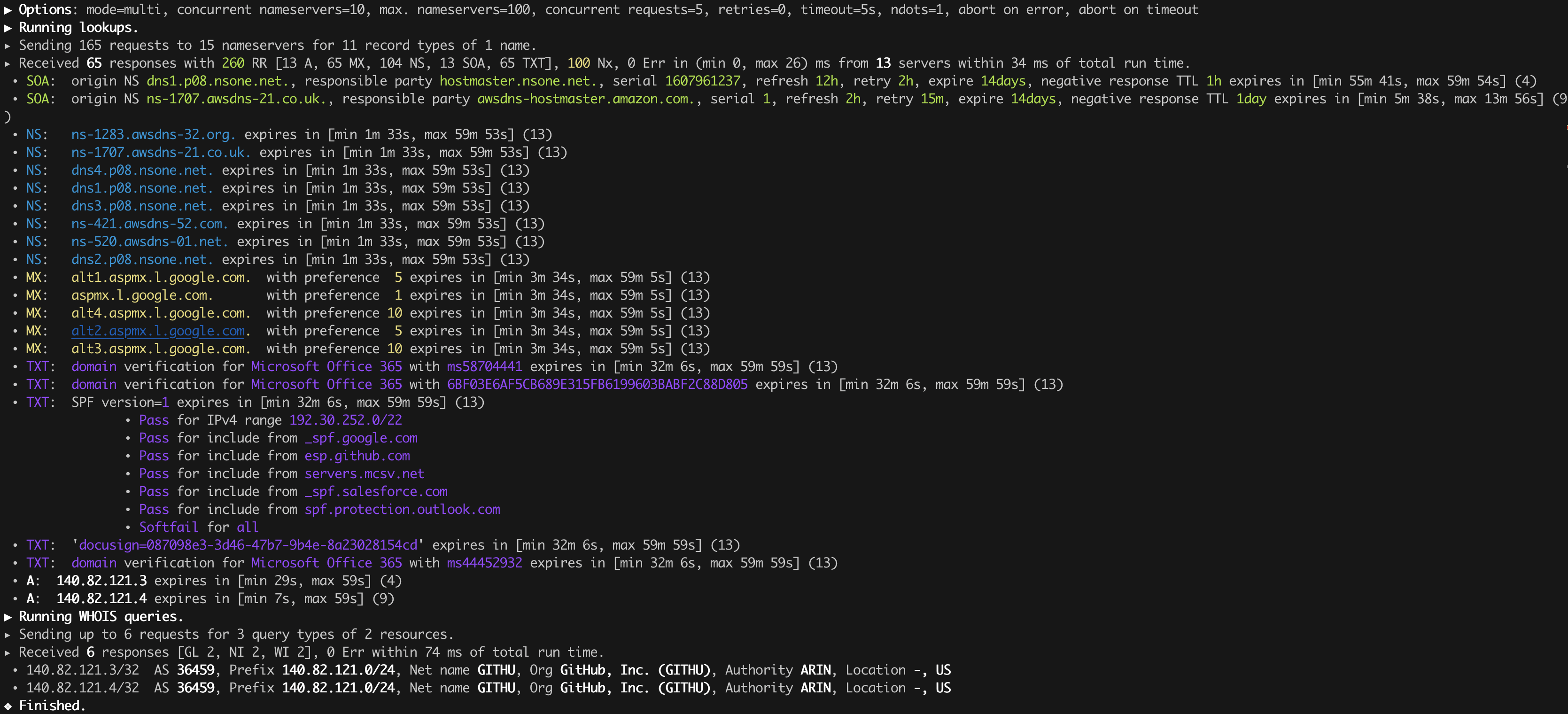
Query all 20+ record types and include WHOIS information for every IP address in the results.
Profile an Entire Domain
mhost -p domain-lookup example.com # ~42 well-known entries
mhost -p domain-lookup --all example.com # ~68 entries (extended set)
One command queries the apex plus dozens of well-known subdomains: email auth (DMARC, MTA-STS, BIMI, TLS-RPT), SRV services (IMAP, SMTP, CalDAV, XMPP, Matrix, ...), DANE/TLSA records, and more.
Discover Subdomains
mhost -p d github.com
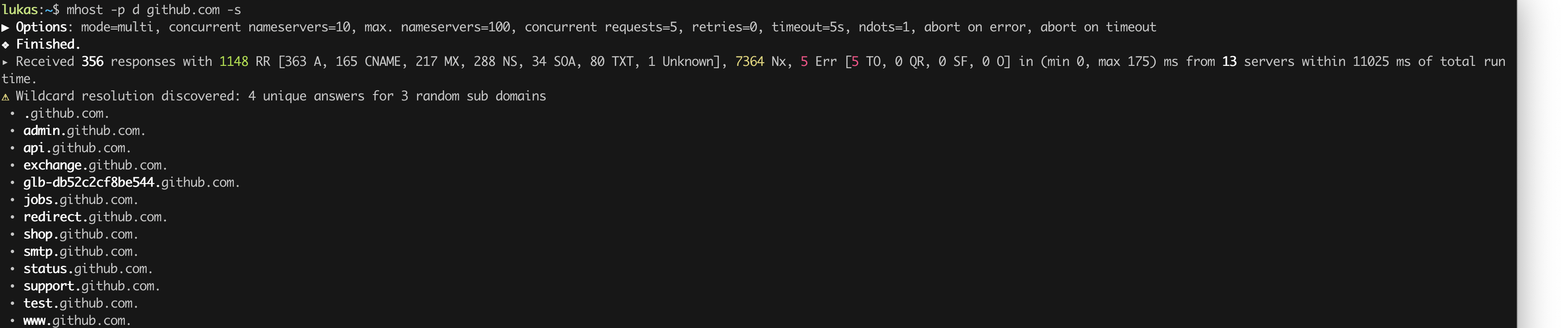
mhost chains 10+ discovery strategies automatically:
- Standard DNS record lookups
- Certificate Transparency logs (crt.sh)
- TXT record mining for referenced domains
- SRV service probing
- Wildcard detection via random subdomain probes
- Zone transfer (AXFR) attempts
- NSEC walking
- Wordlist brute force (424 built-in entries, or supply your own with
-w) - Subdomain permutation on discovered names
- Recursive discovery on found subdomains (
--depth 1..3) - Reverse DNS lookups on discovered IPs
Explore autonomous systems
mhost -p l --all -w github.com
mhost -p l --all 140.82.121.0/24
Validate DNS Configuration
mhost -p c github.com
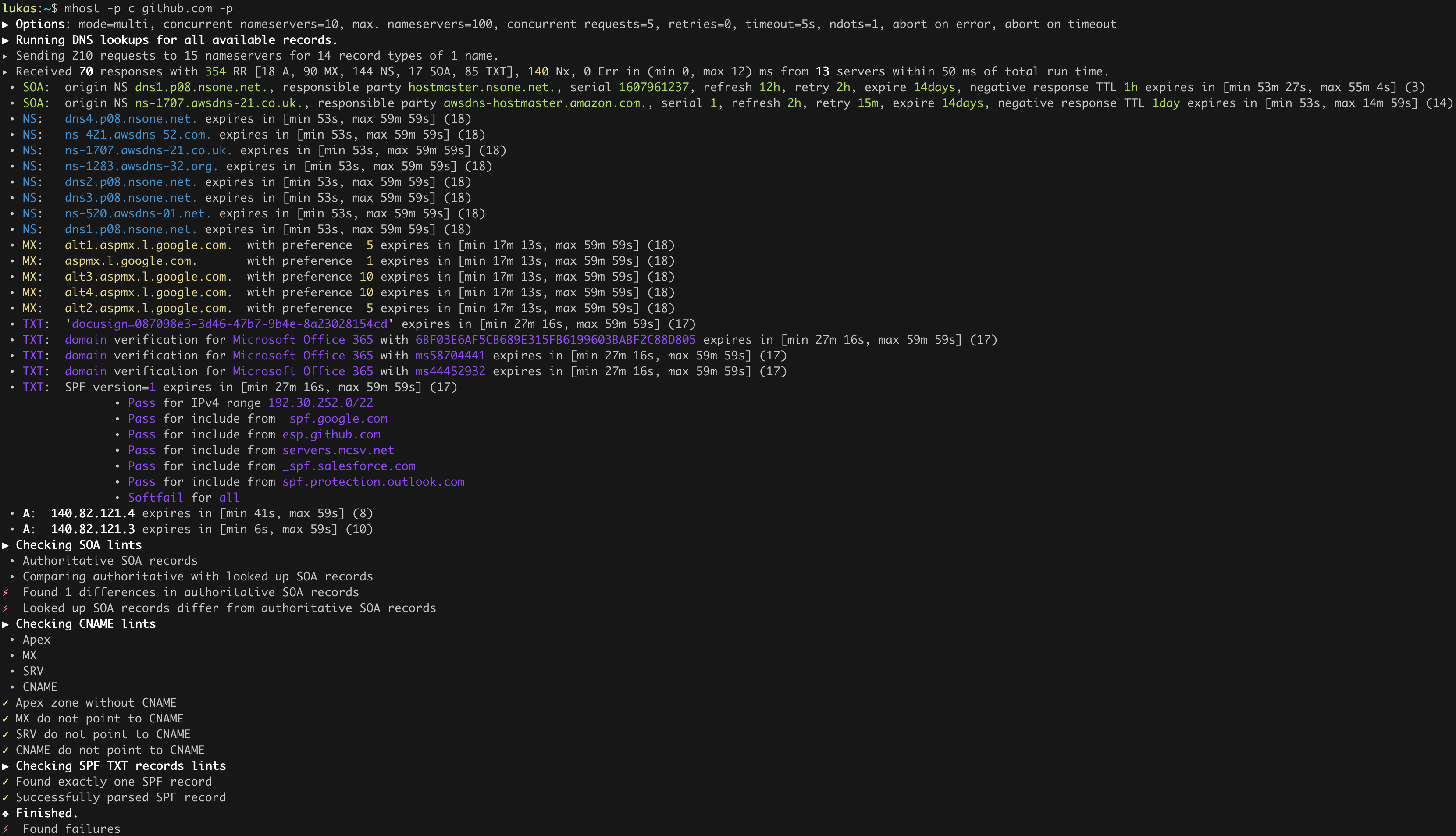
The check command runs 13 lints against a domain's DNS records:
| Lint | What it checks |
|---|---|
| SOA | Start of Authority record validity |
| NS | NS delegation, lame delegation, network diversity |
| CNAME | CNAME usage rules |
| MX | Null MX, duplicate preferences, target resolution |
| SPF | SPF record syntax and policy |
| DMARC | DMARC policy validation |
| CAA | Certificate Authority Authorization tags |
| TTL | TTL consistency across records |
| DNSSEC | DNSSEC presence and configuration |
| HTTPS/SVCB | Service binding record well-formedness |
| AXFR | Zone transfer exposure |
| Open Resolver | Open resolver detection |
| Delegation | Delegation consistency |
Disable any lint individually: --no-soa, --no-spf, --no-dnssec, etc.
Trace the Delegation Chain
mhost trace example.com
mhost trace -t AAAA --show-all-servers example.com
Unlike dig +trace which queries one server per hop, mhost's trace queries all nameservers at each delegation level in parallel. It detects referral divergence (where different root/TLD servers disagree), reports per-server latency, and resolves missing glue records automatically.
Check DNS Propagation�
mhost -p propagation example.com
mhost -p prop --all example.com
After making a DNS change, check whether it has reached all the major public resolvers. Uses the predefined nameserver set (Cloudflare, Google, Quad9, Mullvad, Wikimedia, DNS4EU).
Diff Records Between Nameservers
mhost diff --left 8.8.8.8 --right 1.1.1.1 --all example.com
Compare what two different nameserver sets return for the same domain. You can also diff against saved JSON snapshots:
# Save a snapshot
mhost lookup -s 8.8.8.8 -q -t A,AAAA,MX example.com --output json > before.json
# Later, diff snapshot against live DNS
mhost diff --left-from-file before.json --right 1.1.1.1 example.com
# Or compare two snapshots offline
mhost diff --left-from-file before.json --right-from-file after.json example.com
Verify DNS Against a Zone File
mhost verify example.com.zone
Compares every record in a BIND zone file against live DNS and reports matches, mismatches, and missing records. Non-zero exit code on mismatch for CI/CD integration.
# Verify against your authoritative nameserver
mhost -s ns1.example.com verify example.com.zone
# Check propagation to public resolvers
mhost -p verify example.com.zone
# Strict mode: also flag TTL differences
mhost verify --strict example.com.zone
# Only check mail-related records
mhost verify --only-type MX,TXT example.com.zone
# CI one-liner
mhost verify zones/example.com.zone || notify_team "DNS drift detected"
Look Up Record Type Info
mhost info # List all supported types
mhost info MX # Details about MX records
mhost info SPF # Details about SPF TXT sub-type
mhost info _dmarc # Details about the _dmarc well-known subdomain
Built-in reference with summaries, details, and RFC references for every supported record type, TXT sub-type, and well-known subdomain.
JSON Output
Every command supports --output json for machine-readable output:
mhost -q --output json l --all example.com | jq .
mhost -q --output json trace example.com | jq '.hops[] | .zone_name'
mhost -q --output json c example.com | jq '.results[] | select(.status != "Ok")'
mdive -- Interactive TUI
mdive is an interactive terminal UI for exploring DNS. Type a domain, watch records stream in from multiple servers in real time, then drill into anything interesting.
mdive example.com # Dive right in
mdive -p example.com # Use 84 public resolvers
mdive -s 8.8.8.8 -s 1.1.1.1 example.com # Pick your own nameservers
What you get:
- Live, sortable record table -- apex plus dozens of well-known subdomains across 10 categories, with progressive streaming and a real-time progress bar
- Drill-down navigation -- press
lto follow CNAMEs, Enter to dive into subdomains, Backspace to go back (likecdandcd ..for DNS) - Five discovery strategies -- press
dfor CT logs, wordlists, SRV probing, TXT mining, and permutation - DNS health checks -- press
cfor 9 lint categories with color-coded pass/warning/fail results - WHOIS and geolocation -- press
wfor AS numbers, network prefixes, organizations, and countries for all IPs - Server response dashboard -- press
sfor per-server latency stats (protocol, OK/error counts, min/avg/max) - Regex filtering -- press
/and type a pattern to filter across names, types, and values - Vi-style navigation --
j/k,gg/G, digit-prefixed commands, Tab to cycle grouping modes